6.8 KiB
Introduction
Welcome to our comprehensive guide on configuring Identity Provider (IdP) for users and groups synchronization. This document provides step-by-step instructions and best practices for setting up and managing your synchronization processes effectively.
Google WorkSpace
Before you start creating and configuring an Google Workspace application, ensure that you have the following:
- User account with admin permissions: You must have an Google Workspace user account with the admin permissions to create and manage Google Workspace applications. If you don't have the required permissions, ask your workspace administrator to grant them to you.
- Create new
NetBirdproject in Google cloud console https://console.cloud.google.com. - Enable
Admin SDK APIforNetbirdproject at https://console.cloud.google.com/apis/library/admin.googleapis.com.
Step 1: Create a service account
- Navigate to API Credentials page
- Click
CREATE CREDENTIALSat the top and selectService account - Fill in the form with the following values and click
CREATE- Service account name:
NetBird - Service account ID:
netbird
- Service account name:
- Click
DONE
Step 2: Create service account keys
- Navigate to API Credentials page
- Under
Service Accountsclick theNetBirdto edit the service account
- Take note of service account email address, we will use it in next steps
- Click the
Keystab - Click the
Add keydrop-down menu, then selectCreate new key - Select
JSONas the Key type and clickCreate
When you create a service account key by using the Google Cloud console, most browsers immediately download the new key and save it in a download folder on your computer. Read how to manage and secure your service keys here
Step 3: Grant a user management admin role to a service account
- Navigate to Admin Console page
- Select
Accounton the left menu and then clickAdmin Roles - Click
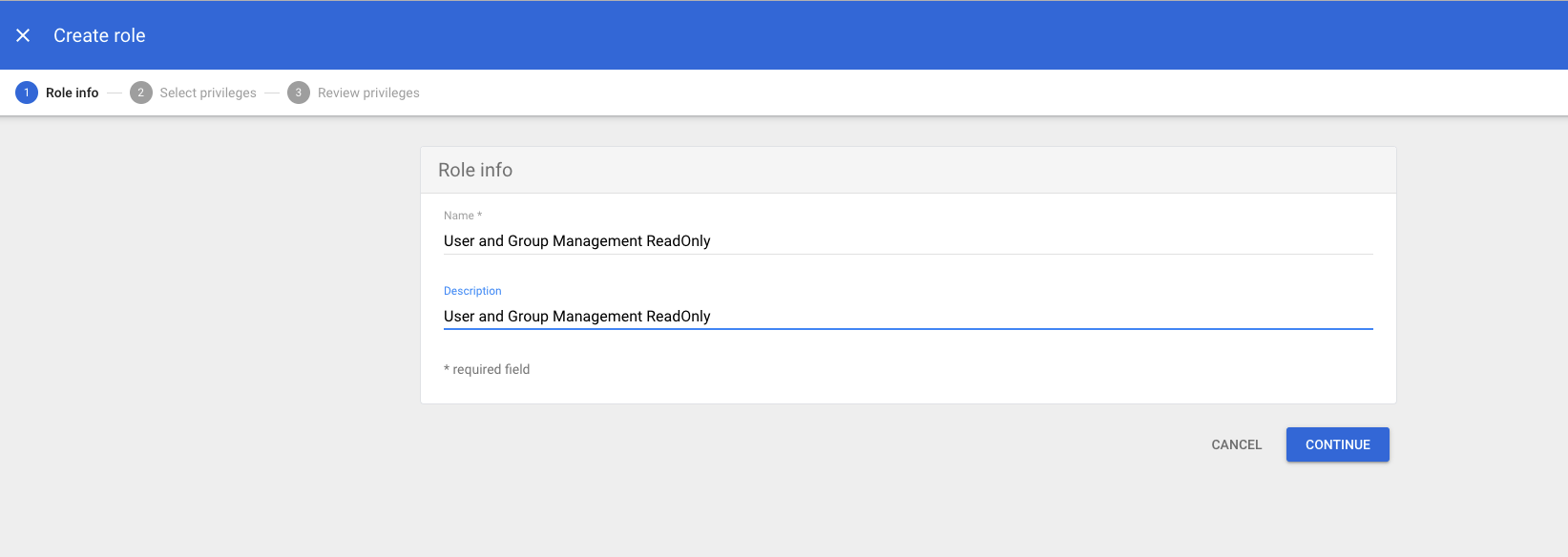
Create new role - Fill in the form with the following values and click
CREATE- name:
User and Group Management ReadOnly - description:
User and Group Management ReadOnly
- name:
- Click
CONTINUE
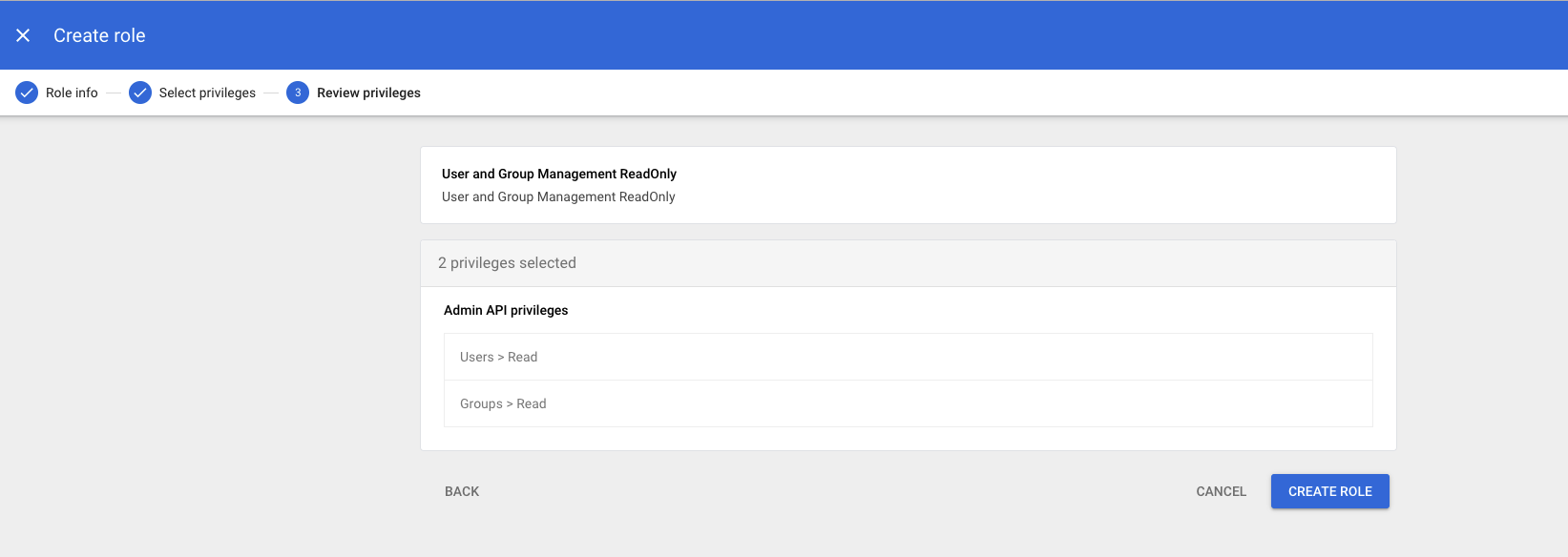
- Scroll down to
Admin API privilegesand add the following privileges- Users:
Read - Groups:
Read
- Users:
-
Verify preview of assigned Admin API privileges to ensure that everything is properly configured, and then click
CREATE ROLE -
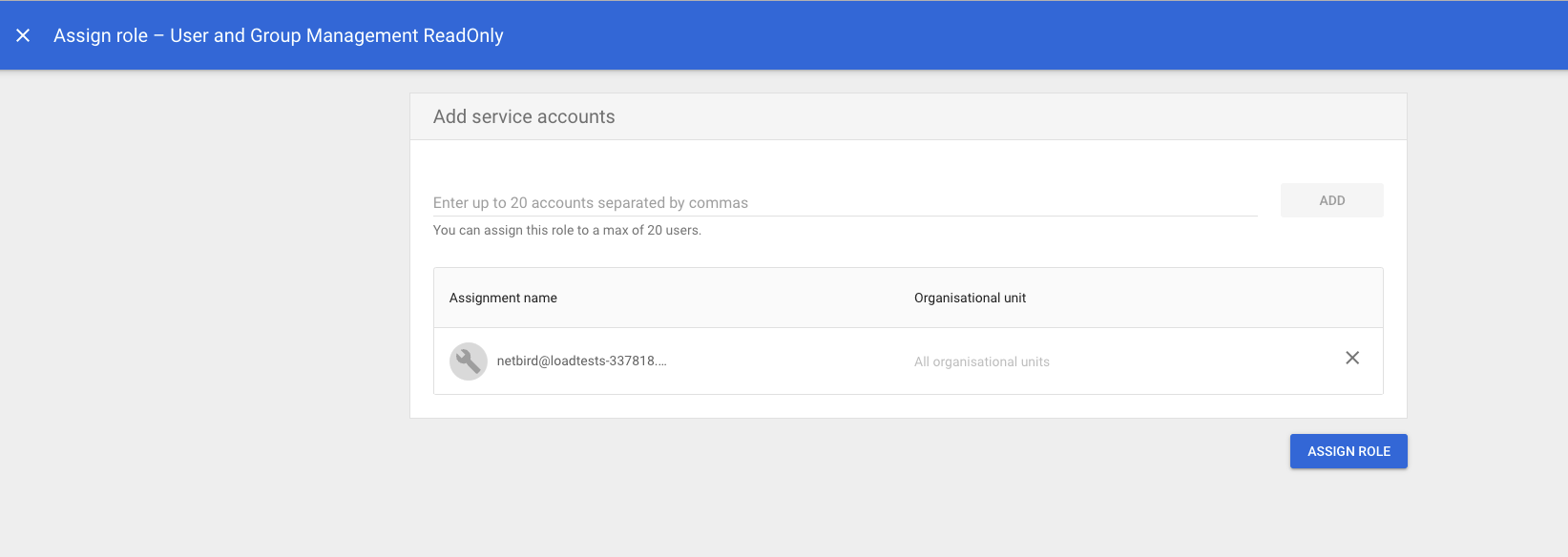
Click
Assign service accounts, add service account email address and then clickADD
- Click
ASSIGN ROLEto assign service account toUser and Group Management ReadOnlyadmin role
- Navigate to Account Settings page and take note of
Customer ID
Azure AD
Before you start creating and configuring an Azure AD application, ensure that you have the following:
- User account with admin permissions: You must have an Azure AD user account with the appropriate permissions to create and manage Azure AD applications. If you don't have the required permissions, ask your Azure AD administrator to grant them to you.
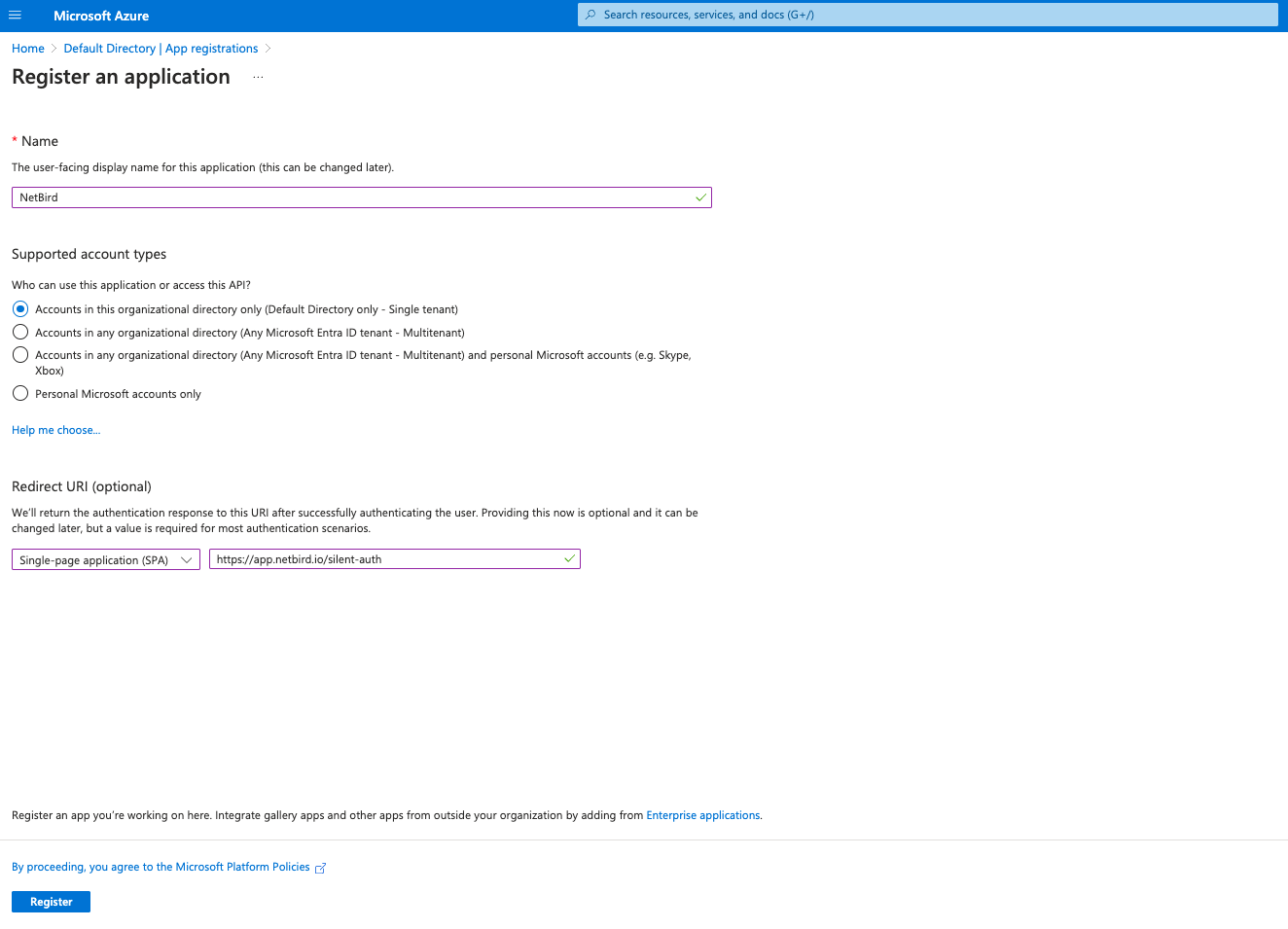
Step 1. Create and configure Azure AD application
- Navigate to Azure Active Directory
- Click
App Registrationsin the left menu then click on the+ New registrationbutton to create a new application. - Fill in the form with the following values and click
Register- Name:
NetBird - Account Types:
Accounts in this organizational directory only (Default Directory only - Single tenant) - Redirect URI: select
Single-page application (SPA)and URI ashttps://app.netbird.io/silent-auth
- Name:
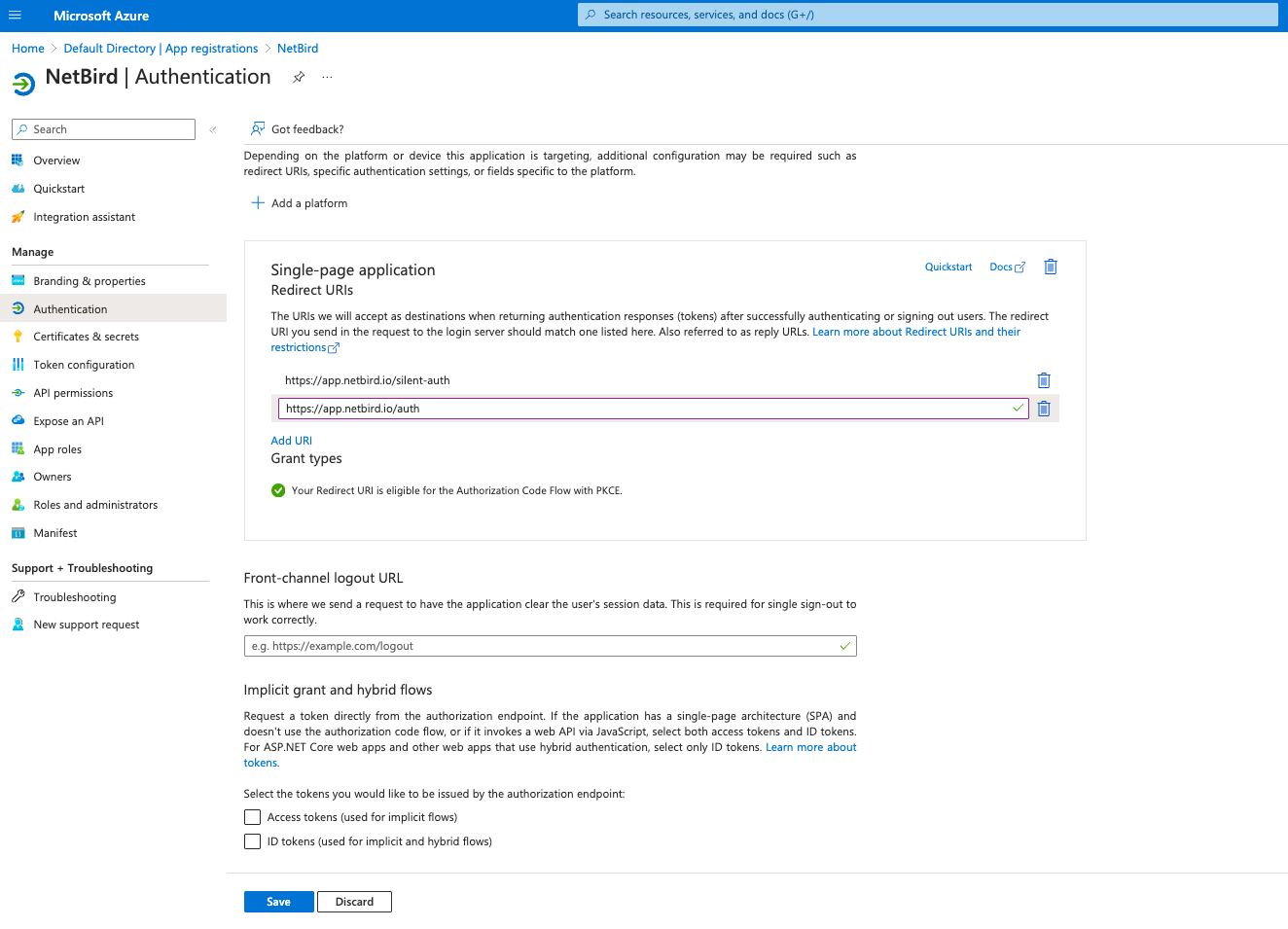
Step 2. Platform configurations
- Click
Authenticationon the left side menu - Under the
Single-page applicationSection, add another URIhttps://app.netbird.io/authand clickSave
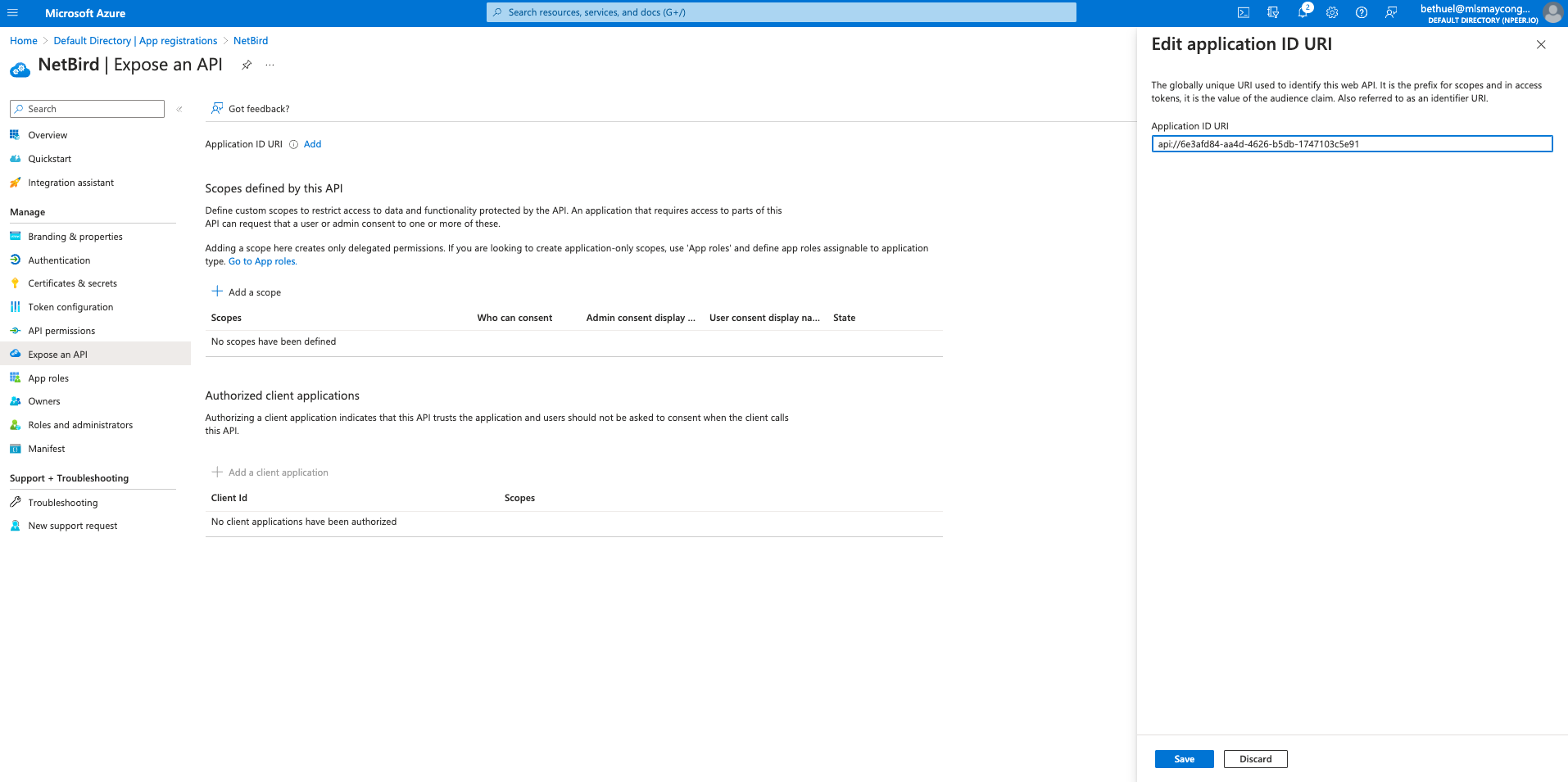
Step 3. Create a NetBird application scope
- Click
Expose an APIon the left menu - In
Application ID URIclickAddand thenSave
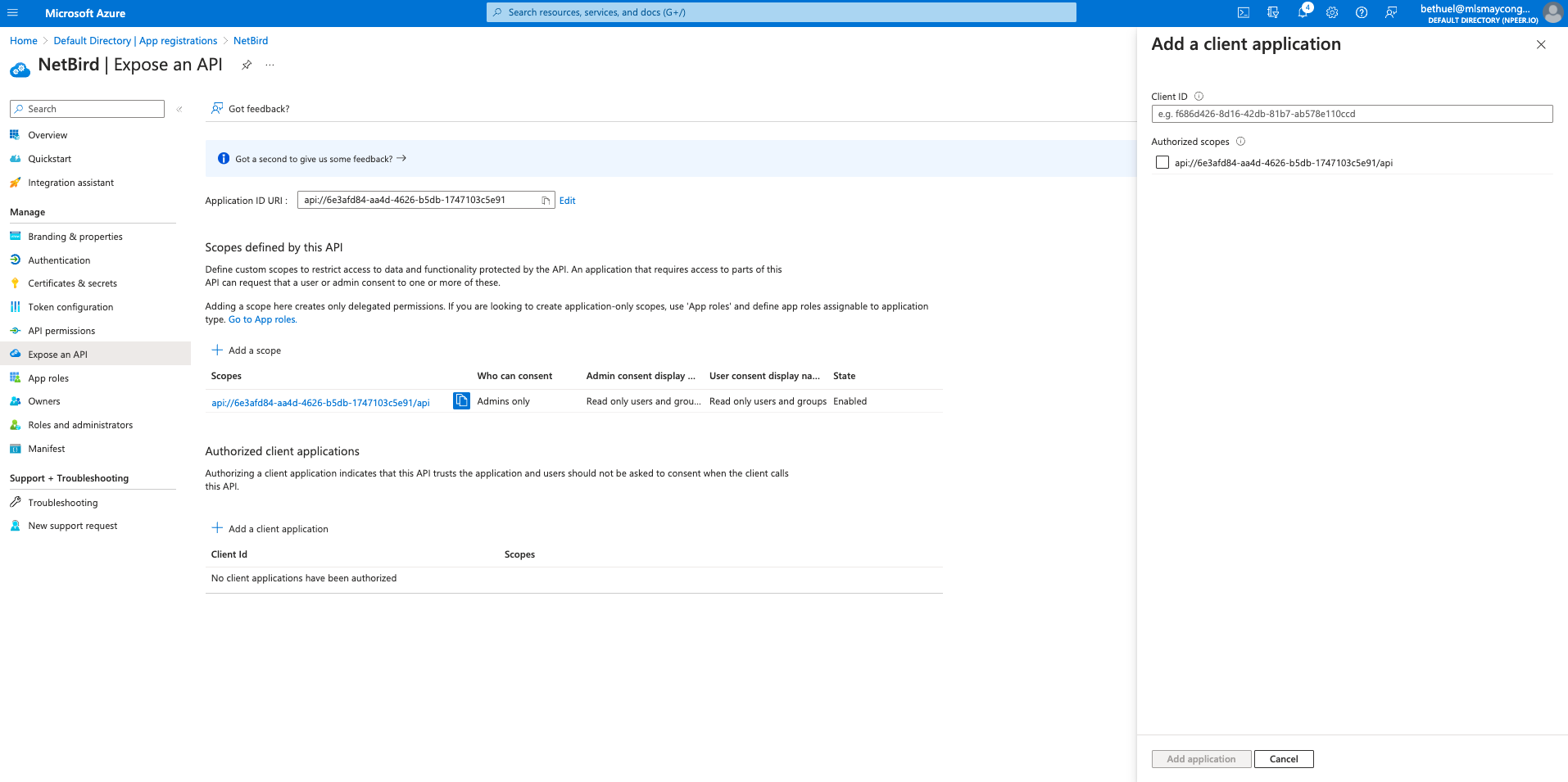
- Under
Scopes defined by this APIclick+ Add a Scope - Fill in the form with the following values and click
Add scope- Scope name:
api - State:
Enabled
- Scope name:
- Under
Authorized client Applications, click on+ add a client applicationand enter the following: - Fill in the form with the following values and click
Add application - Client ID: same as your Application ID URI minus the
api://
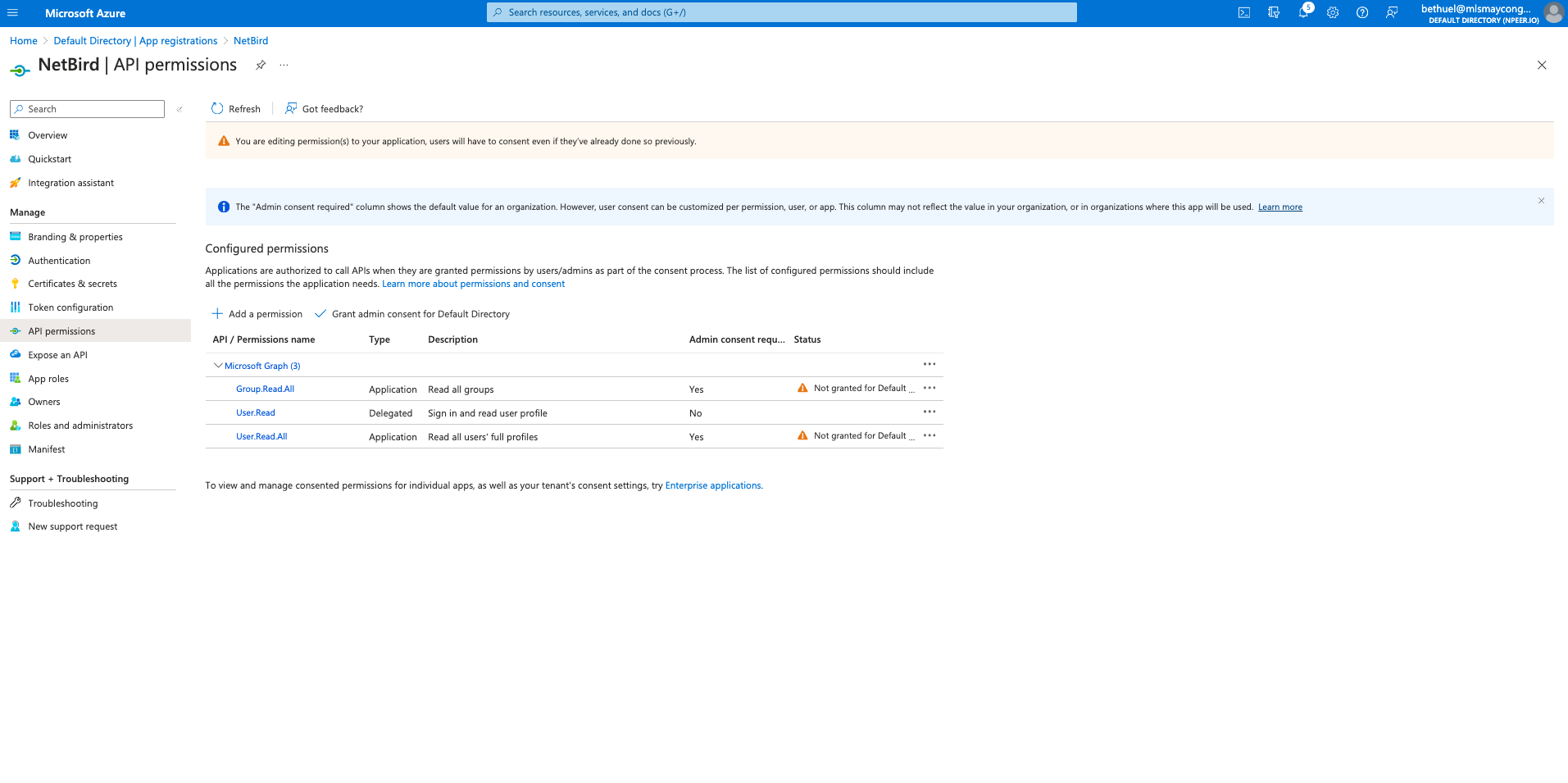
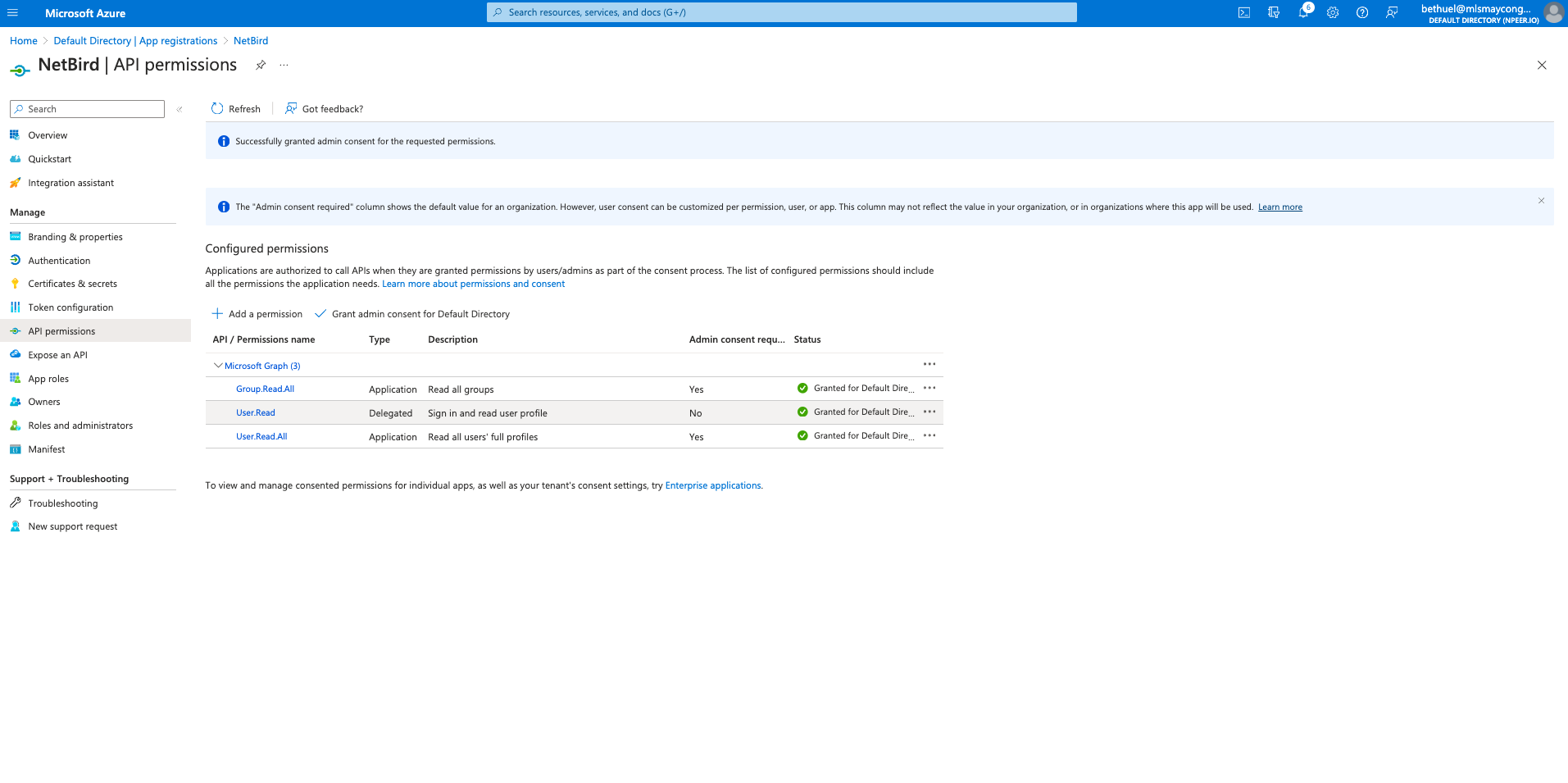
Step 4. Add API permissions
- Click
API permissionson the left menu - Click
Add a permission - Click
Microsoft Graphand then clickApplication permissionstab - In
Select permissionsselectUser.Read.AllandGroup.Read.Alland clickAdd permissions
- Click
Grant admin conset for Default Directoryand clickYes
Step 5. Update token version
- Click
Manifeston left menu - Search for
accessTokenAcceptedVersionand change the value fromnullto2 - Click
Save
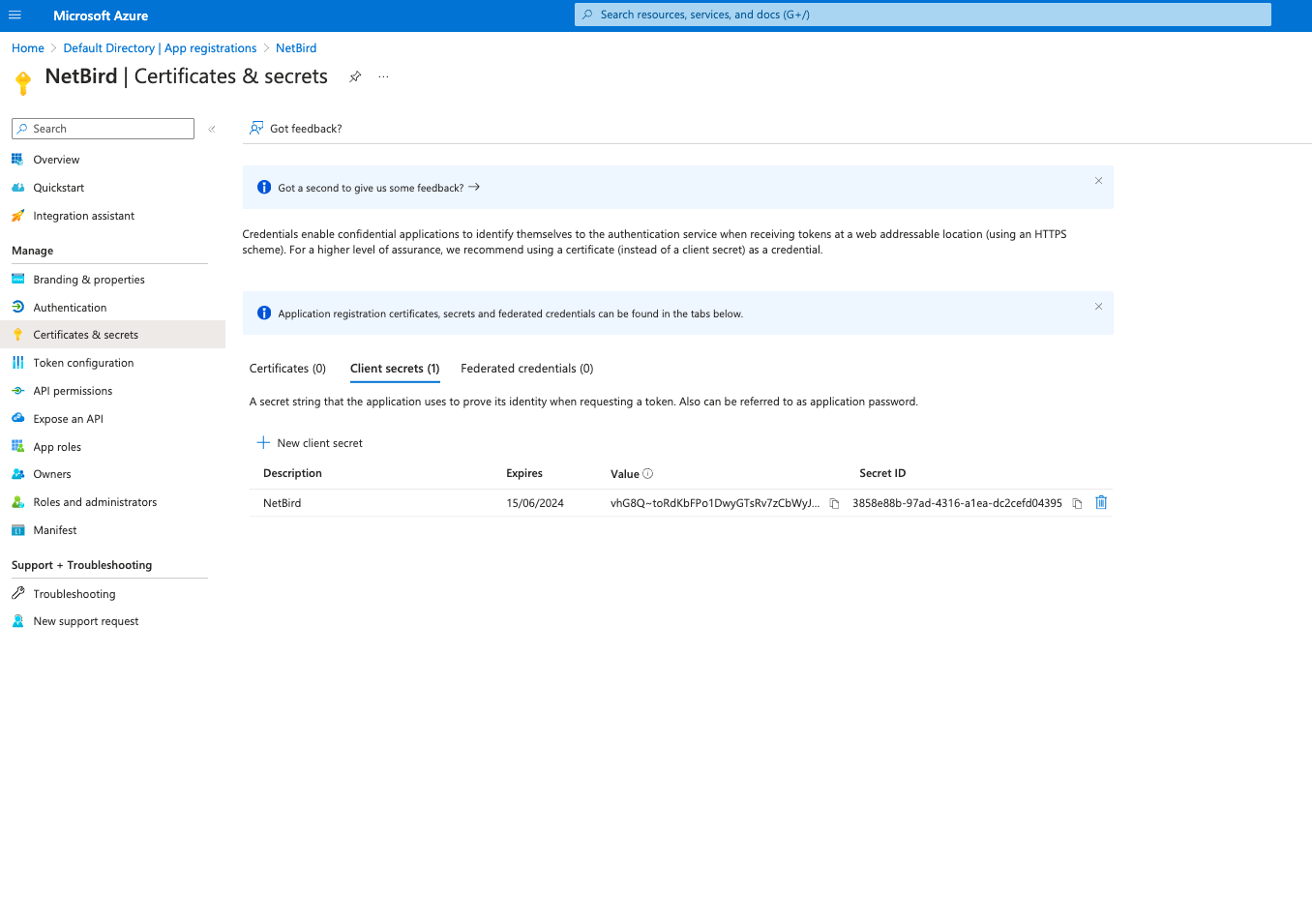
Step 6. Generate client secret
- Click
Certificates & secretson left menu - Click
New client secret - Fill in the form with the following values and click
Add - Description:
NetBird - Copy
Valueand save it as it can be viewed only once after creation.
- Navigate to Owner applications.
- Select
NetBirdapplication in overview page, take note ofApplication (client) IDandDirectory (tenant) ID.